Introduction
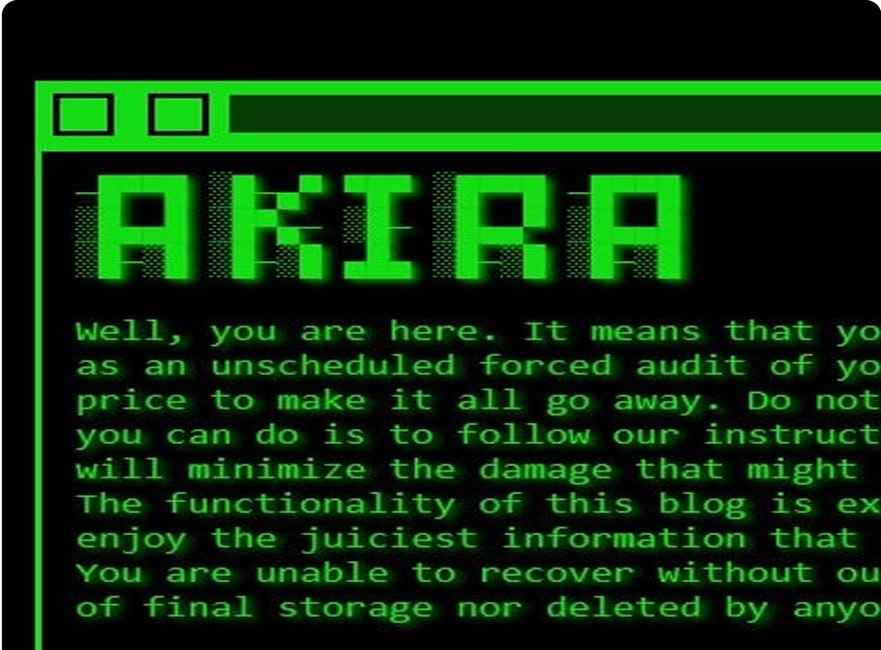
We will move our discussion ahead from our last topic on Ransomware and will go through a ransomware Akira. In the crowded and ever-evolving ransomware landscape, Akira has quickly established itself as one of the most disruptive players. Emerging in March 2023, Akira targets organizations with a double extortion playbook — exfiltrating sensitive data before encrypting systems, forcing victims into a pay-or-leak dilemma.
Its cross-platform capabilities (Windows, Linux, ESXi) and rapid evolution, including a Rust-based variant dubbed Megazord, have made it a growing concern for sectors worldwide.
Akira is a Ransomware-as-a-Service (RaaS) family first observed in 2023 and highly active through 2024–2025, responsible for many incidents across industries and regions. It typically performs data exfiltration followed by encryption (double-extortion). CISAVeeam Software
Primary access vectors
- Compromised remote access (VPN/RDP) and stolen credentials are frequently used to gain initial access. Several incidents have been associated with exploited or misconfigured VPN appliances (SonicWall and others). TechRadar+1
- Phishing and commodity access brokers also supply initial footholds to Akira affiliates. Qualys
Post-compromise behavior (observed TTPs)
- Reconnaissance: AD discovery, share enumeration, and host/network scans. CISA
- Credential harvesting & lateral movement: Use of Mimikatz-like techniques, abuse of RMM and Windows admin tools (PSExec, WMI). CISA
- Security disabling: Attempts to disable or tamper with Microsoft Defender/EDR and backup services. Some reports describe a driver-based technique to alter Defender settings. TechRadar
- Exfiltration: Use of rclone, cloud storage services, uploads to FTP/SFTP, or TOR for exfil before encryption. Picus SecurityQualys
- Encryption: Windows, Linux, and ESXi variants have been observed; often hybrid crypto (symmetric per file, asymmetric key wrapping). Picus Security
Notable operational features
- Akira operators run a leak site and use double extortion. They are affiliate-driven (RaaS) and have hit MSPs to maximize impact.
The Timeline and Tactics
Akira’s operations are believed to have roots in the Conti ransomware lineage — evident from overlaps in coding style and operational patterns.
Key Traits of Akira’s campaigns:
- Initial Access: Often via compromised VPN, RDP, or other remote access services.
- Reconnaissance: Active Directory enumeration, file share mapping.
- Exfiltration: Targeted theft of sensitive intellectual property and business data.
- Encryption: Hybrid AES + RSA model, appending distinctive extensions (e.g.,
.akira). - Extortion: Threatening public leaks on a dark web portal.
By early 2024, Akira had claimed over 250 victims and extorted $42 million globally.
Major Breaches That Made Headlines
1. KNP Logistics — A 158-Year-Old Giant Brought Down
In mid-2023, KNP Logistics, a UK-based transportation company founded in the 19th century, faced a devastating Akira ransomware attack.
- Root Cause: Investigations revealed a single weak password was exploited to gain a foothold.
- Impact:
- All core systems and backups were encrypted or destroyed.
- Operations ground to a halt.
- Despite having cyber insurance, the ransom demands were deemed “unpayable.”
- The company was forced into permanent closure, resulting in 700 job losses.
- Business Lesson: Even well-established companies can collapse overnight without robust password policies, network segmentation, and resilient backups.
2. Nissan Australia — Customer Data Exposure
In December 2023, Nissan Australia became another high-profile name on Akira’s victim list.
- Scope: The attackers claimed to have stolen 100,000 customer records, including personal details and vehicle information.
- Operational Impact: Service disruptions, security audits, and a lengthy recovery period.
- Reputation Hit: A major automotive brand’s trust was shaken, and regulatory scrutiny followed.
- Business Lesson: Large enterprises must prioritize zero-trust architectures and continuous monitoring to prevent compromise through user accounts or third-party integrations.
3. Stanford University — Academic Data Breach
Stanford University confirmed in 2023 that approximately 27,000 records had been stolen during an Akira incident as well.
- Targeted Data: Academic and administrative records.
- Risk: The exposure of sensitive personal and institutional data could lead to phishing, identity theft, and long-term privacy concerns for students and staff.
- Business Lesson: Academic institutions, often with diverse and distributed IT environments, require rigorous endpoint hardening and network segmentation to mitigate risk.
Technical Anatomy of Akira Encryption
Akira typically uses hybrid encryption:
- AES (symmetric key) for encrypting files quickly.
- RSA (asymmetric) for encrypting the AES key, making decryption without the private key nearly impossible.
- Appends extensions like
.akirato encrypted files. - Deletes shadow copies and backup restore points also.
Safe Pseudocode — Non-Executable
# PSEUDOCODE (NON-EXECUTABLE) — Illustrative only
function main():
# 1. Preliminary checks/locking (attempts to avoid multiple runs)
if already_running_lock_exists():
return
# 2. Build exclusion list (system folders, user-specified safe paths)
exclusions = [
"C:\\Windows",
"C:\\Program Files",
"C:\\Program Files (x86)",
"C:\\Users\\Public\\Downloads",
"C:\\Backup",
... # additional environment-specific exclusions
]
# 3. Generate per-host symmetric key (fast encryptor)
host_sym_key = generate_random_bytes(32) # e.g., 256-bit AES key
# 4. Wrap symmetric key with attacker_public_key
wrapped_host_key = asymmetric_wrap(attacker_public_key, host_sym_key)
# 5. Persist wrapped key for later ransom negotiation
save_wrapped_key_to_file("KEYINFO."+random_id, wrapped_host_key)
# 6. (Optional) Exfiltrate files before encryption
if exfiltration_enabled():
files_to_exfil = collect_high_value_files(root_paths, exclusions, top_n=1000)
exfiltrate_files(files_to_exfil, exfil_destination)
# 7. Disable or attempt to disable restore mechanisms (logical call)
attempt_disable_shadow_copies() # try to delete Volume Shadow Copies
attempt_stop_backup_services() # logical; actual method varies
# 8. Enumerate files for encryption
files = enumerate_files(root_paths, exclusions, file_filters)
# 9. For each file, stream encrypt and atomically replace
for file_path in files:
try:
if should_skip(file_path, exclusions):
continue
# read file in safe chunked manner (avoid memory blow-up)
temp_encrypted = encrypt_file_chunks(file_path, host_sym_key, chunk_size=65536)
# securely move/rename original to backup location OR overwrite
atomic_replace(file_path, temp_encrypted)
rename_file(file_path, file_path + ".AKIRA") # sample extension
except Exception as e:
log_error(e, file_path)
continue
# 10. Drop ransom note
drop_ransom_note_on_desktop_and_root("README_AKIRA.txt", ransom_instructions)
# 11. Optionally clean traces and exit
clear_temp_artifacts()
exit()
Notes about the pseudocode:
- Functions like
attempt_disable_shadow_copies()andexfiltrate_files()are placeholders to show behavior; they are intentionally non-specific. - The point is to show control flow so defenders can map behavior to detections (file enumeration, chunked I/O, atomic swap, renaming with extension, dropping ransom note).
Typical file targeting & exclusions
Akira-like encryptors usually:
- Target documents, databases, Office files, image/video, code, and backups (
*.docx, *.xlsx, *.pst, *.mdb, *.sql, *.tar, *.zip, *.mdb). - Exclude system files, OS folders, and some AV/product files to reduce instability and detection noise.
- May use inclusion rules (file masks) and size thresholds (skip very large system files or small binaries).
Ransom note behavior & key storage
- Further a small file (README, HOW_TO_RECOVER.txt) is placed in each directory and desktop.
- Generally host-wrapped keys are stored locally (so ransomware can prove they encrypted data).
- Eventually Operators post proof / victim data on leak sites if no payment.
In the next post we will discuss how to draft the right detection rule for detecting this attack also. Stay tuned…
Likewise In an year old video Prabh Nair has given a basic explanation on Akira.


