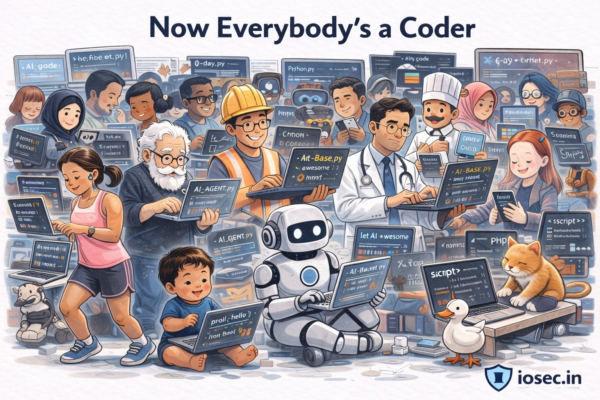
AI Is Flooding Open Source — And Most of It Won’t Survive (2026)
The Pattern Has Been Here Before When AWS made servers cheap, everyone became a cloud startup. When no-code tools made apps cheap, everyone became a founder. Now AI has made writing software cheap — and everyone has become an open source maintainer. The result is the fastest expansion of GitHub repositories in its history. Most…